TABLE OF CONTENTS
What is SCA payment?

What is SCA compliance?

New requirements for authenticating online payments will be introduced in Europe as part of the second Payment Services Directive (PSD2).
Strong Customer Authentication (SCA) is part of PSD2 regulations, mandating certain security measures that needs to be carried out during transactions, in order for a customer to prove their identity more securely before they can grant a third party access to their account.
Regulatory Technical Specifications (RTS) has outlined that two of the three forms of customer authentication should be used. The merchant has to provide card issuers with two independent authentication factors from customers to approve the transaction.
The three authentication factors laid out in the RTS are:
- Knowledge:Something only the user knows(PIN, password, etc)
- Possession:Something only the user possesses (a card, a mobile phone, etc)
- Inherence: Something the user is (biometric, identification like fingerprint, iris or voice recognition

Issuers will vary on whether they support all three authentication factors, and which methods they use for each factor.
September 14, 2019: Official Compliance Deadline for Strong Customer Authentication
Merchants and other players in the payments space need to assess what changes they need to make to be ready by the date of enforcement, September 14, 2019.
The second Payments Services Directive (PSD2) mandated that starting September 14, 2019 online credit card transactions where both the issuing and acquiring banks are within the EEA (EU + Norway, Iceland, and Liechtenstein) must meet Strong Customer Authentication (SCA).
Note: UK regulator granted an 18 month phase-in period (upto March 2021) to give banks and businesses more time to prepare for the new requirements.
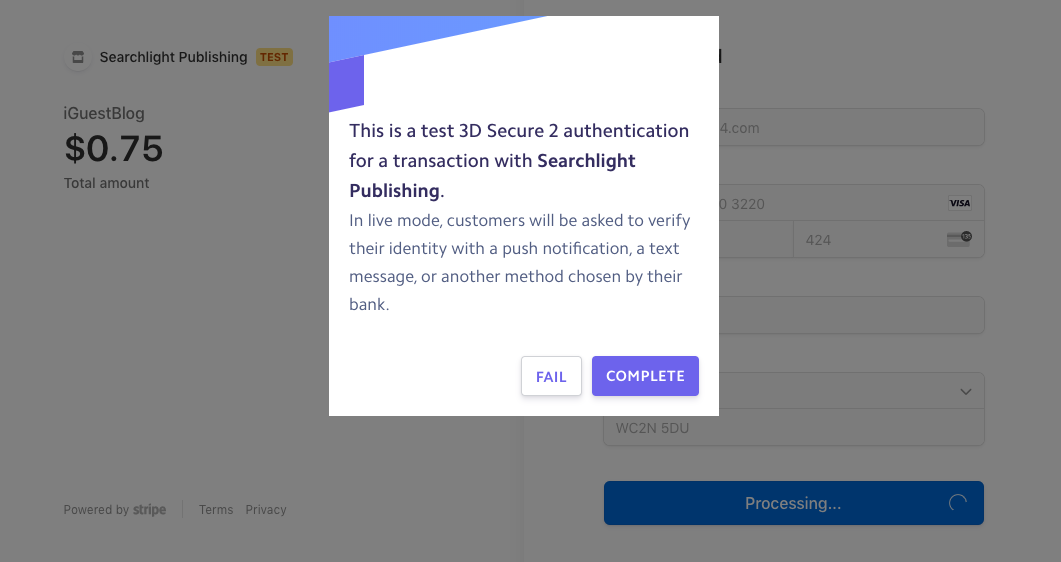
ASKAN’s implementation of SCA:
Paying for subscriptions along with free trail days and onetime product purchase has been implemented for this client.
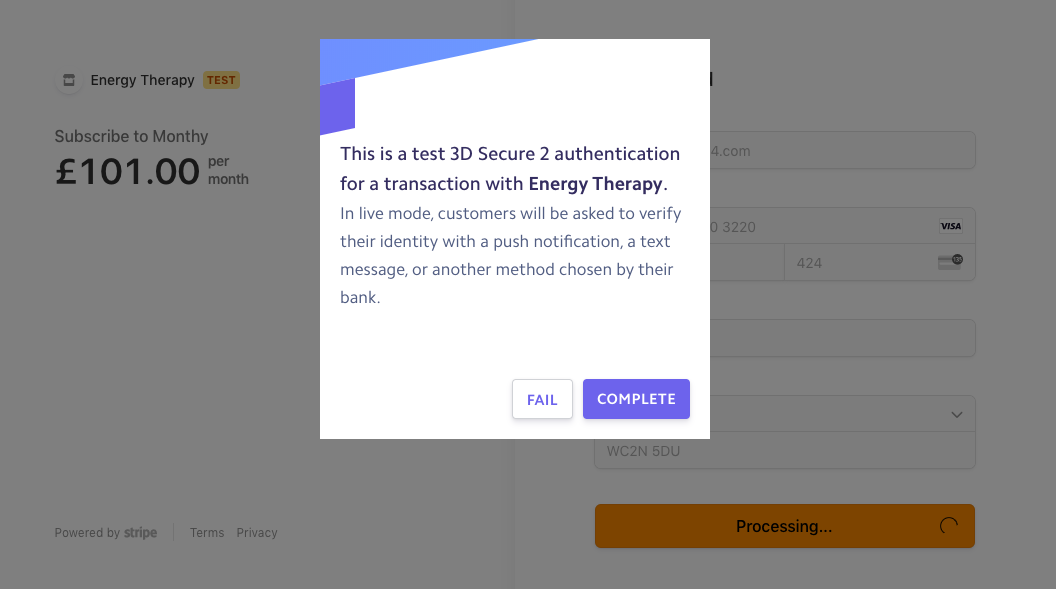
We have implemented onetime purchase of the product along with dynamic pricing plan.
Why should we implement SCA?
Most card payments and all bank transfers will require SCA. Recurring direct debits on the other hand are considered “merchant-initiated” and will not require strong authentication. With the exception of contactless payments, in-person card payments are also not impacted by the new regulation.
For online card payments, these requirements will apply to transactions where both the business and the cardholder’s bank are located in the European Economic Area (EEA).
How to implement SCA?
Authorization server:
It grants scoped access tokens and serves as a token endpoint after validating credentials and attributes of user against the directory.
API intelligence:
It detects threats and aids in blocking suspicious requests by analyzing API request data and learning the normal/abnormal activity patterns.
Resource server:
It stands in front of the exposed financial API’s and redirects API calls to an authorization server. Resource server validates the access tokens that are issued by authorization server, by enforcing policy for requiring at least two of the three required SCA-compliant authentication factors.
Multi-factor authentication:
It prompts the user to prove their identity by enforcing two or more of the necessary security factors.
Customer data governance:
It offers REST APIs for managing identity and authorization data by enforcing customer consent records – an essential requirement in a post GDPR environment.
Identity data store:
IT encrypts and stores user credentials, consent records and other attributes, and scales to handle peak access request volume.
What should we know about authorisation code?
- One-time-use only.
- Information about the elements cannot be derived from it.
- Cannot generate new code based on previous code.
- It cannot be forged.
How to generate an authorisation code?
- If an authentication fails, the incorrect elements shouldn’t be revealed
- Idle time without activity is maximum 5 minutes
- Five failed authentication will lead to temporary block. The duration of block and number of retires will be based on a risk score.
- Authentication sessions must be protected according to common and secure standards of open communication.
What are the exceptions on implementation of SCA?
- Low-risk transactions.
- Contactless Payments below €50.
- Payments below €30.
- Fixed-amount subscriptions.
- Merchant-initiated transactions (including variable subscriptions).
- Secure Corporate payments.
- Unattended Terminals for Transport Fares and Parking Fees.
- Phone sales.
- Credit Transfers between Accounts Held by the Same Natural or Legal Person.
- Trusted beneficiaries.
Most popular pages

From Prototype to Production: The Engineering Checklist That Actually Matters
Prototypes lie. They perform well in demos because they are not doing any of the work that production systems actually do. There is no...
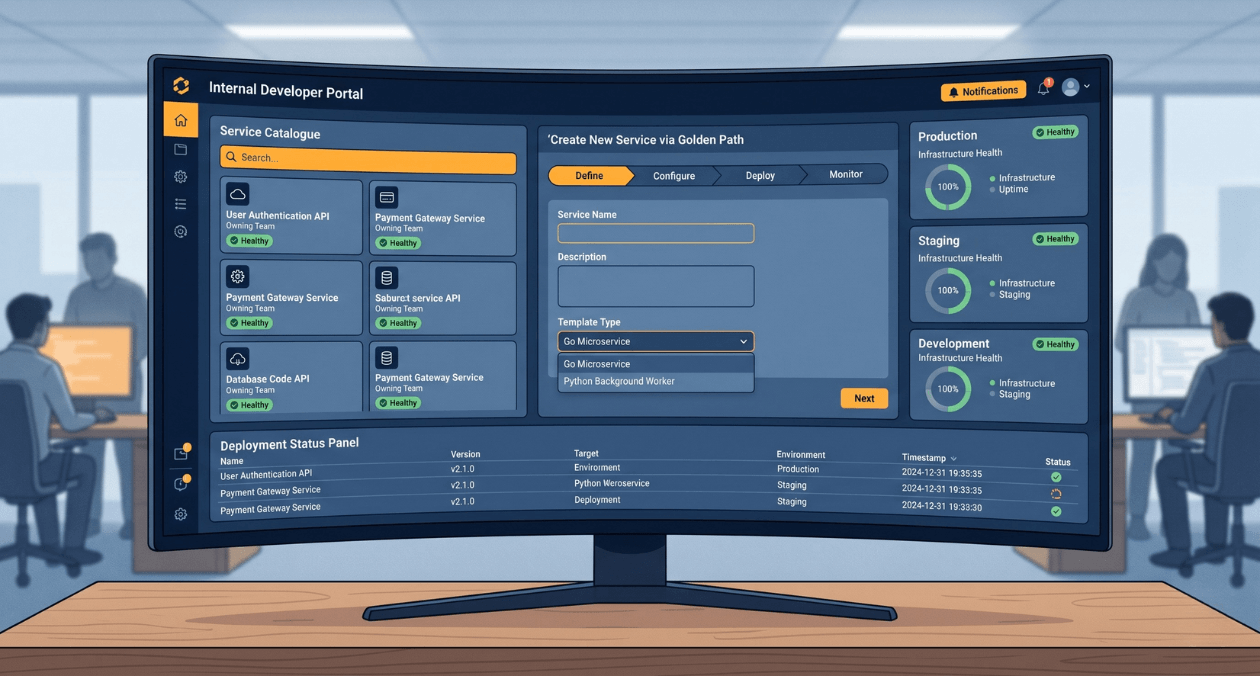
Building a Developer Experience (DX) Platform: From Golden Paths to Self-Service Infrastructure
There is a measurement problem at the heart of platform engineering. The people who benefit most from a well-built internal developer platform are often...
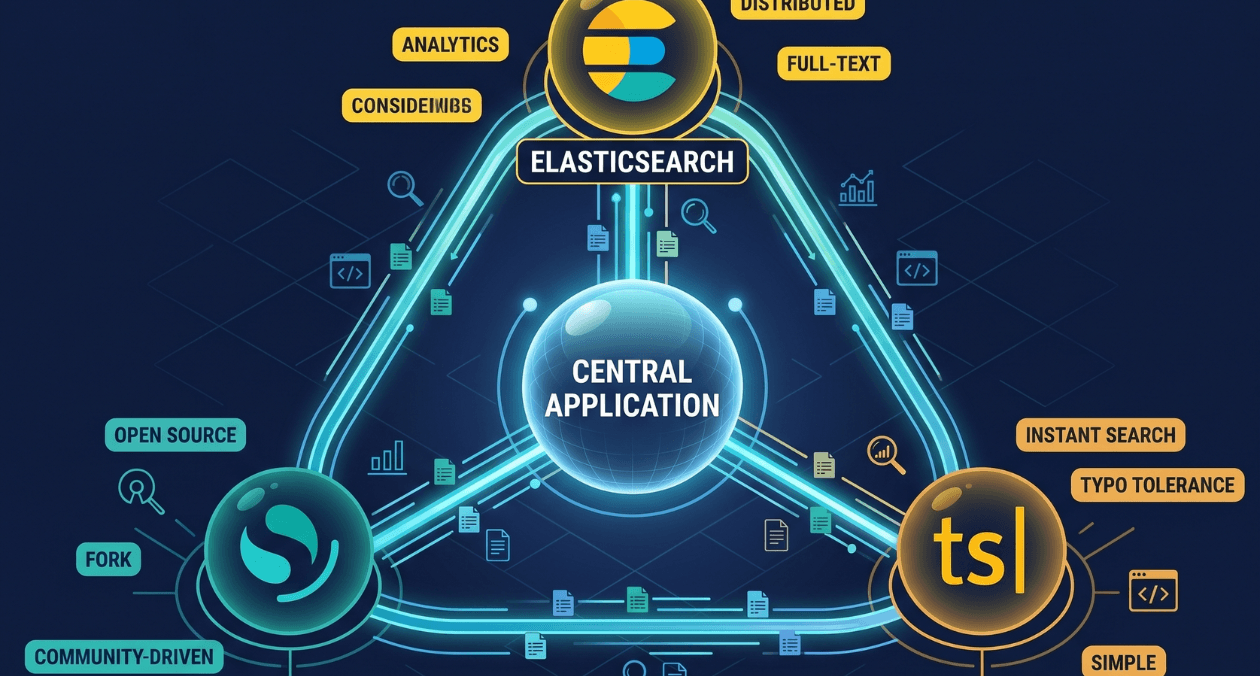
Search Infrastructure for Applications: Elasticsearch vs OpenSearch vs Typesense
Search is one of those features that seems straightforward until you try to build it properly. A basic LIKE query handles small datasets. The...


